So hello everyone, welcome back to Gossipfunda. Today we are back with another interesting topic – How does Google Authenticator work?
Tech giants like Google, Amazon, etc. are very serious about security. This grows as we progress every day. The need of maintaining and upgrading security measures is going up. This is because more and more people are joining and getting accustomed to the technology. This is also giving rise to people whom we call the “bad guys”. They are basically black hat people using technology to carry out fraudulent tasks like forcefully installing malicious software into others’ systems, stealing sensitive credentials like passwords and other bank details. These are some of the reasons why authentication and verification( like hacked phones) of every user account on any platform is important.
What is an Authenticator?
To start with, let’s have a formal definition of Authenticator. An authenticator is a tool that performs authentication, which is basically verification of the identity of the concerned individual. Digital authentication is the process by which the user authenticates to a computer system or app. Authentication is generally checked by simple passwords that the user sets. Or, there may be specific questions that require case sensitive answers (that the user sets while signing up to the app). Nowadays, we see the most secure form of authentication, that is using One Time Password (OTP). It’s the most secure unless the “bad guy” has your device with him.
What is Google Authenticator?
Google Authenticator is a software from Google. It implements two-step verification services. These services are based on two algorithms:
- Time-based One time password algorithm (TOTP)
- HMAC-based One time password algorithm (HOTP)
Almost all of the Google services include Google Authenticator. Not only limited to that though, Google Authenticator also supports third-party applications that use it for authenticating its users. When you log in to such an app or site, the Authenticator generates a six to eight-digit OTP (one-time-password). This OTP is sent to the respective email of the user (or associated verified phone number). You need to enter this OTP along with your usual login credentials to successfully log in.
Don’t miss: What is com.android.incallui
Purpose of Google Authenticator (Two-step verification)
This two step verification is very important when you have enterprise details or other pieces of stuff associated with your Google account. To make sure of the fact that only someone who comes to know (or guesses) your password cannot log in, this two-step verification is done. It bids for the entry of an OTP that comes only to your device. Hence, it adds an extra layer of security to your account. It is always recommended to turn on two-step verification process for every application that requires creating an account with credentials.
Use Case of Google Authenticator
The app running the Google Authenticator must first be installed on your device. To log in to the site, you provide your username and password (that you set while creating the account). The site then computes a six digit One Time Password. Note that, this OTP is only computed and not yet displayed on the screen. You are then prompted to enter the OTP. You have to access the OTP through the Authenticator app. The Authenticator app independently computes the same OTP and displays it. You can now check it and type into the site where you are trying to log in. Immediately, you will be logged into the site.
Hence, as you can see, just knowing your username and password won’t allow someone to break into your account. The OTP will only be sent to your phone which you use. So the attacker also needs the physical address of your device that is running the Authenticator application.
See also: uicc unlock
How does Google Authenticator work?
As said earlier, the Authenticator implements Time-based One Time Password (TOTP) algorithm. The following ingredients are what it has:
- A Shared Secret: The shared secret is something that you need to set up the account. The account we are talking about now is the account on our phone. The secret can either be entered manually by you, or you may scan a QR code using your phone camera.
- Input (Current Time): Once you have obtained the secret from the server, no further interaction is required. The input time is the value you get from your phone. However, it is very important to have your phone’s time accurate. This is because the server will repeat what happens on your device. This is done according to the current time that the server knows. You may set your device time to Network-set time so that you don’t need to bother much about it.
- Signing Function: HMAC-SHA1 is the signing function used. HMAC is a well-known algorithm using a secure one-way hash function (SHA1 here) to sign a value. And if you’re curious about what HMAC stands for, then it’s Hash-based Message Authentication Code.
If you are a code enthusiast, go through the pseudo code of the OTP algorithm:
| original_secret | xxxx | |
| secret | BASE32_DECODE(TO_UPPERCASE(REMOVE_SPACES(original_secret))) | |
| input | CURRENT_UNIX_TIME() / 30 | a constant value is set for a period of 30 seconds |
| hmac | SHA1(secret + SHA1(secret + input)) | apply hashing |
| offset | hmac[len(hmac)-1] & 0x0F | the Last nibble |
| four_bytes | hmac[offset : offset+4] | make a subset of 4 bytes from 20 bytes |
| large_integer | INT(four_bytes) | for converting four bytes to integer |
| small_integer | large_integer % 1,000,00 | this gives a six digit code |
A Technical Description – What happens behind the scene?
During its setup, an 80-bit secret key is generated for each user. This generation is done by the Service Provider. The Authenticator gets the secret key when it is transferred. Now, this transfer is done like 16, 26, or 32 character base32 string. Also, most of the time it is transferred as a QR code.
The HMAC-SHA1 hash value is calculated as soon as the Authenticator app is opened. The secret key performs a major role in this hash calculation. The HMAC-ed message for instance:
- The number of 30-second periods since the Unix epoch (in case of TOTP)
- Or, a counter that’s incremented every time with new code (in case of HOTP)
Do you know about: com.tmobile.pr.adapt
How to set up Google Authenticator in your phone?
Now that we know a couple of facts about the Google Authenticator, how it works, and a part of its pseudo code, let’s see how you can set it up on your phone.
- Firstly, download the Google Authenticator from the Apple App Store, or Android Google Play Store (depends on the OS you run).
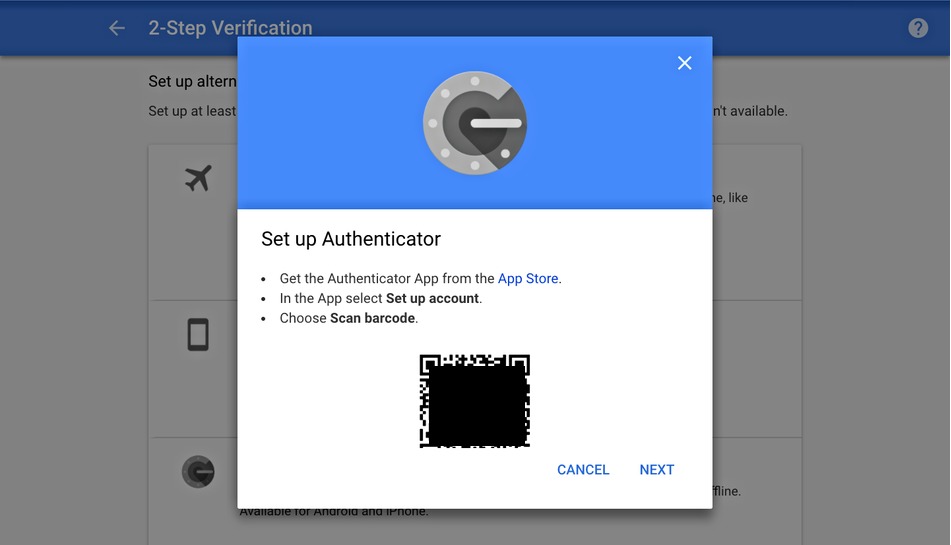
- Now, set up the two-step verification on your Google account. To do this first, log in to your account. Then, under the “Security and Sign-In” section, select “Two-Step Verification.” Now scroll down, locate, and select the “Authenticator App” option.
- In the next prompt, you’re asked to select your phone. The two options are Android and iPhone. Select your device here.
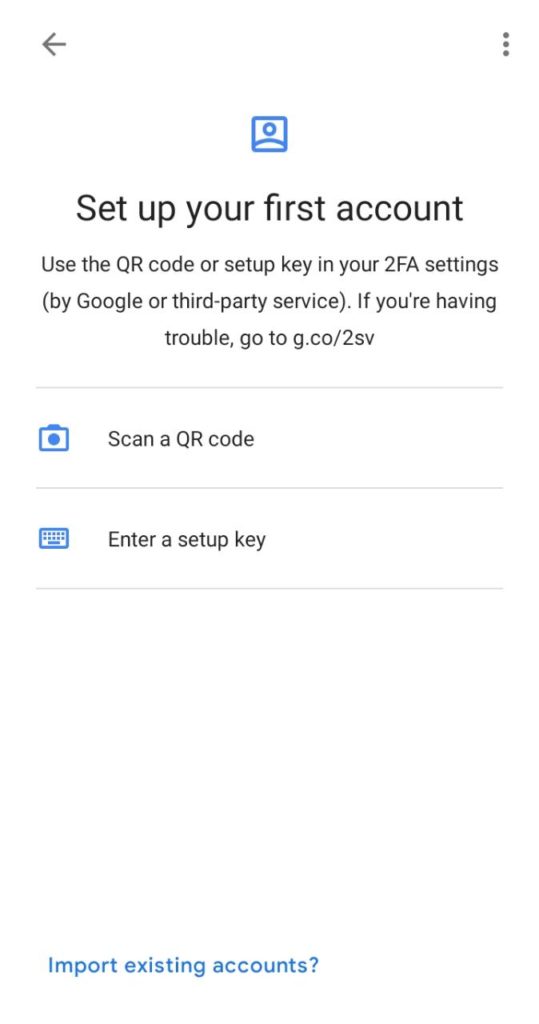
- Then, open the actual Google Authenticator application on your phone. Once it is open, tap on the “Plus” button present at the top right corner of the screen.
- Two options show up at the bottom of your screen. They are “Scan barcode” and “Manual entry.”
- Now, choose any one of these options and you will be able to complete the process. If you use the “Scan barcode” option, you have to download the QR scanner app. After that, you have to point your phone camera at the QR code displayed on your computer screen to verify the Authenticator’s connection with your account. This process usually takes longer to complete.
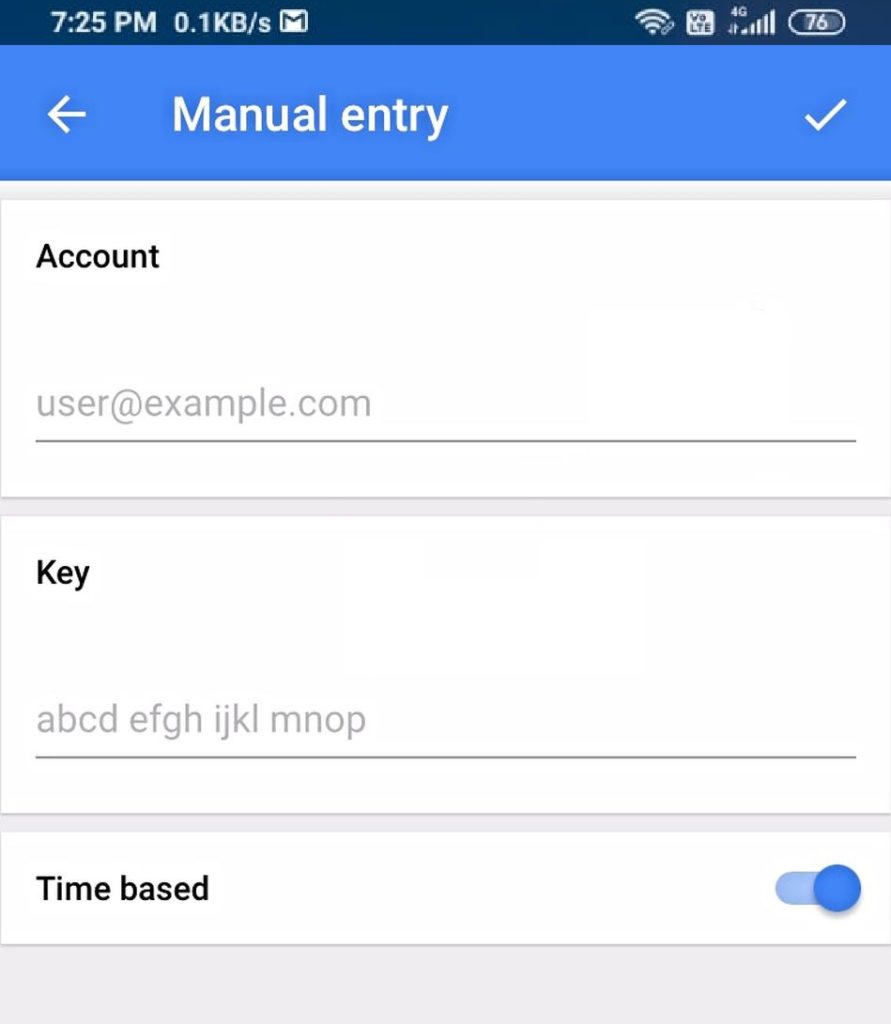
- On the other hand, choosing “Manual entry” would bid Google send you a 16-digit code to an email address. Grab that code and enter it to complete the verification.
Important Notes
There are some things that need your attention, else things may go wrong. The “Time Based” option should be toggled to “ON.” This ensures that the code that you enter is aligned with the Authenticator’s most recently generated passcode.
So from now on, each time you log into the account that’s connected with the Google Authenticator, it will ask you to enter a 6 digit verification code. What you need to do is just open the Google Authenticator app. The app will generate a new randomized six digit code. Grab that code and enter it to get access to your account.
Conclusion
So now it’s time for a farewell. Gossipfunda has discussed about Authenticator, why it’s necessary? Also, We have focussed on how does Google Authenticator work. We have looked through a small pseudo-code of the Google Authenticator. Next, we have known how to set up the Google Authenticator in our device – there are detailed steps that we have given for you to follow. Last but not the least, we have discussed about the importance of two-step verification. It is always recommended to turn on two-step verification for every service you use. As discussed earlier, it adds an extra layer of security. Just knowing your password would not allow an attacker to access your device. This principle is what the Google Authenticator follows, to keep you safe from attackers.

I am a tech enthusiast. I have a keen curiosity in Data Science, Machine Learning, Deep Learning and Neural Networks. I have acquired knowledge in Python, SQL, Java, Amazon Web Services (AWS) and IoT (Internet of Things). I have built a couple of ML models and worked on datasets in IBM Watson Studio. Besides, I take great delight in content writing, which makes me come here, as I believe that this is one of the most reliable techniques for sharing one’s skill.



