Hello everyone, your favorite author is back with another article at Gossipfunda.com. This time I’m back again with another interesting Android package called com.sec.omadmsp. As always we’ll be looking into every nook and cranny of this package. Pulling out all the cords and carefully studying them. We’ll be talking about what this package is used for and if this package is safe for your Android device.
Is it safe to remove this package? We’ll also be looking into the entity that built this package known as OMA. Looking into OMA’s history we’ll also be talking about its purpose in the Mobile Industry. So without wasting another minute, let’s jump into it.

Introduction
As always, if you’re reading this article you must have encountered the “com.sec.omadmsp” package somewhere or the other. It might be in your Google Activity logs or it might be while exploring ES File Explorer. Encountering the package name for the first time must’ve been confusing since it doesn’t look anything like the normal packages. Something com.android.mms or com.facebook.katana at least gives you a brief idea about what this package might be used for. That is not the case with com.sec.omadmsp. This is why today I’ll be talking to you guys in detail about everything this package is used for. But first, we’ll be starting with some information about the organization that built this package OMA.
Open Mobile Alliance
aka the OMA is a standards body. The Open Mobile Alliance develops the open standards for the mobile industry. Very much like the ITU, which sets the standards in the communication world. OMA decides on the specifications which should be common all across the industry. To better understand it, think of it as IUPAC in the field of chemistry just not funded by the government. Just like the IUPAC decides the worldwide standards for things like nomenclatures and such in the field of Chemistry. Only OMA is more like a forum where the industry stakeholders agree on a common specification.
Founded in June 2002, more than 18 years ago. The OMA has its headquarters in San Diego, California, USA. OMA was created to deal with the numerous industry forums that were each dealing with different protocols. This caused a huge number of problems since each of these forums had a different set of rules. Leading to duplication of work, overlapping of release schedules, etc. The OMA was created to group all these forums under one organization.
Members of the OMA include the industry’s traditional mobile and equipment manufacturers such as Nokia, AT&T, Ericsson, Orange, T-Mobile, Verizon, etc.
Specifications:
The different specifications maintained by the Open Mobile Alliance are:
- Browser and Content, previously called WAP browsing. The most recent version relies on XHTML Mobile Profile.
- MMS for multimedia messaging.
- Digital Rights Management standards, also called OMA DRM.
- OMA LwM2M the device management protocol for Lightweight devices.
- OMA-DM the device management protocol for heavier mobile devices. It is more structured than LwM2M.
- OMA IMPS, the protocol is used for instant messaging on mobile devices,
And many more. OMA specifications have also been an inspiration for the NGSI-LD API and information model. It’s specified by the ETSI based on OMA specifications.
Adapting the OMA standards is voluntary to the manufacturers. The current General Manager for the OMA at the time of writing is Seth Newberry.
Device Management
Device management is one of the biggest problems that Mobile Device manufacturers have to go through. Each manufacturer was using its protocol and device management software. This software is the only thing that enables the manufacturer to keep tabs on their devices. Things like software/firmware update, remote configuration, etc.
The variation of different device management software did not make things easy for the industry. This led to the development of a standard device management model known as OMA-DM.
Protocols:
Some other device management protocols are:
- OMA Lightweight M2M (LwM2M): The device management protocol was also developed by the Open Mobile Alliance. Specifically designed for low-end devices the protocol is lightweight, fast, and structured. More than 25 companies have implemented the LwM2M protocol. These include ARM Pelion, AT&T IoT solutions, AVSystem’s Coiote Platform, among others. You can learn more about the LwM2M protocol here.
- OMA-DM: The protocol is more structured and complex than the LwM2M protocol. Meant for Mobile Applications the protocol is useful for changing systems like IP addresses.
- TR-069: This protocol was created by the Broadband Forum. First released in 2004, the protocol is used by hundreds of thousands of devices all over the world. Although not used for mobile devices, TR-069 was developed for heavier use. More complex, and heavily structured than the other two, the protocol is used by Telecommunication devices like Routers, etc. You can learn more about the TR-069 protocol here.
core functionalities:
Some of the core functionalities of the device management protocols include:
- Ensuring user equipment is configured to the standards.
- Updating applications, equipment, functions, etc.
- Monitoring and tracking equipment.
- Remote Troubleshooting of equipment.
Over-the-air programming is considered the main component of Mobile Device Management. This includes commands for changing the settings, troubleshooting the device, etc.
OMA Device Management
The device management protocol was specified by the Open Mobile Alliance DM (Device Management) and DS (Data Synchronization) groups. OMA-DM was designed mainly for the management of mobile phones, tablets, PDAs, etc. OMA-DM uses XML for information exchange. The protocol is more heavily structured than LwM2M and less structured than TR-069 which makes it perfect for use with medium-sized handheld devices. OMA-DM is intended for:
- Configuring the device. This includes the ability to enable/disable a feature.
- Changing the configuration of the device.
- Providing software updates including bug fixes.
- Reporting errors.
This is where the package “com.sec.omadmsp” comes into play.
Since the OMA-DM was designed for mobile devices it takes care of things like limited bandwidth or wireless connectivity, excessive memory, and storage usage, and security vulnerabilities.
The communication between the OMA-DM server and client is a little complex. The server first tries to make contact with the client via any of the methods available such as WAP Push or SMS. The Server tries to make contact with the client by sending a message in the form of SMS. After the client-server connection is established, it might take a series of additional messages for a maintenance task to be completed.
com.sec.omadmsp
The package in question for this article was also developed by the Open Mobile Alliance to aid their OMA-Device Management protocol. com.sec.omadmsp enables the OMA-DM server to perform over-the-air programming on the mobile device. This is why the package com.sec.omadmsp is a very significant package for your OS.
Is com.sec.omadmsp spyware?
Although at first glance it might look like it, but no. In order to search for updates or report some errors or maybe just a general status report, the OMA-DM server uses this package to contact the client. That might sound fishy but rest assured the information always remains in safe hands and is only used for maintenance purposes. This is exactly the reason why com.sec.omadmsp might have appeared on your Google Activity log.
Fix Errors related to com.sec.omadmsp
Most of the errors presented by the package go away automatically but that is not always the case. In fact, some errors can pest you even after a factory data reset. In short, this is why the most reliable method for getting rid of these errors is by getting rid of the package using ADB.
ADB also known as Android Debug Bridge is a PC command-line tool, which is used by devs for controlling their android smartphones.
Simple Steps to fix
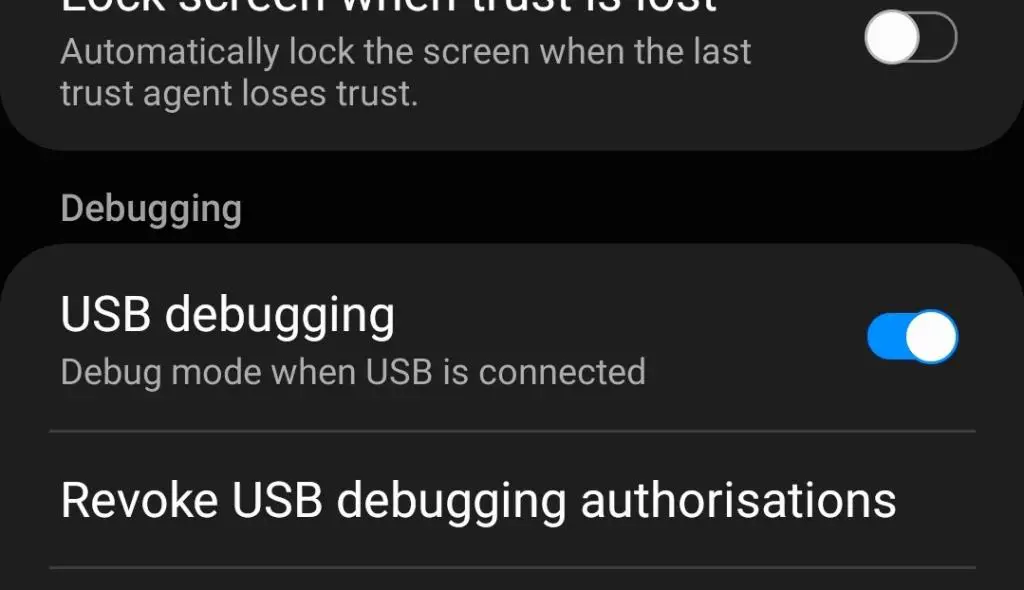
- First, you’re gonna have to enable USB debugging from the developer options in your phone’s settings.
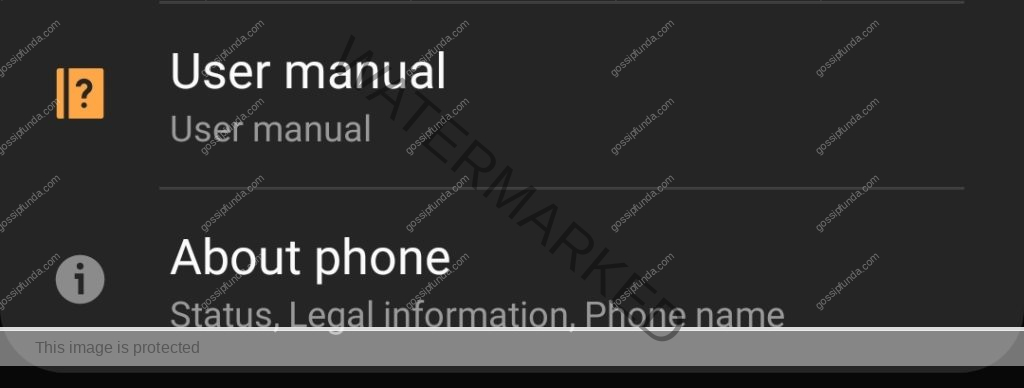
- You can enable Developers Options by going to the About section of your smartphone.
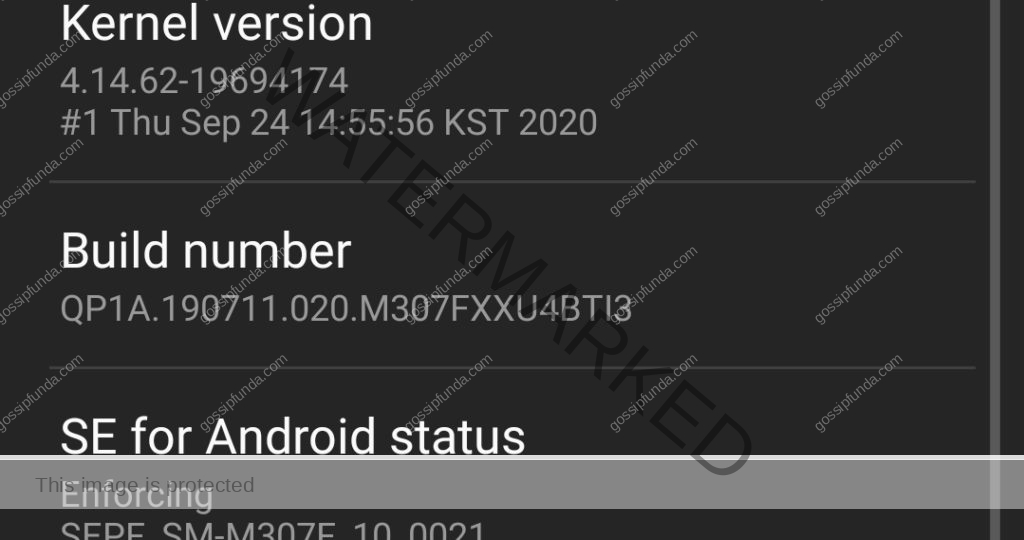
- Now tap on the Build Number field seven times. This will enable the Developers Options
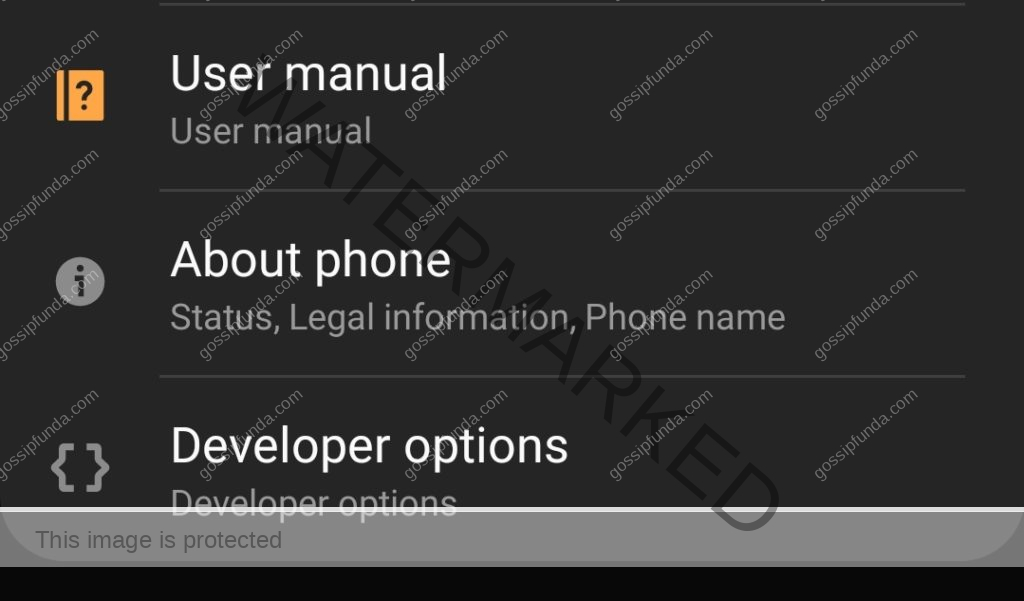
- Go to the developer options from the settings menu and scroll down to find USB Debugging.
- Now you need to open up your PC and set up ADB,
- You can use this link to download ADB. This will download a zip file.
- Extract the zip file in a well-specified folder.
- Meanwhile, Browse into the contents of the folder open up a Powershell or CMD window in that location. You can do this by pressing Shift + Right Click and selecting Open Powershell Window here.
- Type the command: .\adb devices
- This will turn on the ADB Daemon services. Now connect your Android smartphone to your PC. On the android phone, you might need to allow USB debugging for this PC.
- Now run the command .\adb devices again. If the command outputs a serial number on the screen, it implies your smartphone is now connected..
- For removing the packages we will have to enter the ADB Shell. To do this enter: .\adb shell
- The following commands will remove the respective packages one by one:
| pm uninstall -k –user 0 com.sec.omadmspr pm uninstall -k –user 0 com.sec.omadmspr.syncmlphoneif pm uninstall -k –user 0 com.sec.omadmsp |
As a result, this will get rid of the error.
To clarify, remember by using this method, you will not be able to get substantial software updates sent by the OMA-DM server. Hence use this method if and only if it’s necessary.
Conclusion
With that, we’ve come to the conclusion of yet another article. This time we dove deep into the world of Device Management protocols and their working. So, We started off by learning about the Open Mobile Alliance, the forum responsible for setting the standard specifications in the Mobile world. Also, we talked about its history, its purpose, and the specifications maintained by it. Then we moved on to the subjects of Device Management Protocols. On the other hand, We learned about different types of DMs including their aimed devices and different features. Talking about LwM2M, OMA-DM, and the TR-069 we learned about their similarities as well as differences. Moreover, from there we moved on to the main subject of the show “com.sec.omadmsp”. In addition, we talked about its uses and errors. We also talked about how it’s not spyware.
That is going to be all for this article, hope to see you guys again.
Stay Safe.

I am a self-learned coder, and I love reading, writing, and listening all about the new and hot tech in the market. I am a big video game fanatic. From 1987’s Metal Gear to 2015’s Metal Gear Solid V I’ve played them all. I first got interested in programming when I played around with the software PC Logo (the one with the turtle). I don’t think a single day has passed since then without me learning something new in this field.


